3/30/2025: Added Exchange SE.
Microsoft keeps track of the currently supported combinations of .NET Framework and Exchange Cumulative Updates at the Exchange Server Supportability Matrix. However, as time progresses, support information for older Cumulative Updates may be removed from the content, and you may need to resort to cached versions of this page or other sources to find it.
This might be problematic for organizations that are not current and need to determine which upgrade path to follow while staying within the boundaries of supported Exchange deployment configurations. For example, you may need to first upgrade to a specific Cumulative Update supported by a newer release of the .NET Framework to upgrade to a later Cumulative Update.
For these situations, the following tables contain the supportability matrix, enhanced with information regarding earlier Cumulative Updates and .NET Framework versions. These will provide you with the supported upgrade paths for older versions of Exchange.
Note: In-place upgrades of the operating system on which Exchange Server runs are not supported and will not work. Also, keep in mind that you cannot mix nodes within the same Database Availability Groups concerning the operating system. New operating system = new Exchange Server installation = new Database Availability Group.
Exchange SE
| .NET | RTM |
|---|---|
| 4.8 | X |
| 4.8.1 | X |
Exchange 2019
| .NET | RTM-CU1 | CU2-CU3 | CU4-CU13 | CU14-CU15 |
|---|---|---|---|---|
| 4.7.2 | X | X | – | – |
| 4.8 | – | X | X | – |
| 4.8.1 | – | – | X | X |
Exchange 2016
| .NET | RTM- CU1 | CU2 | CU3- CU4 | CU5- CU7 | CU8- CU9 | CU10 | CU11- CU12 | CU13- CU14 | CU15- CU23 |
|---|---|---|---|---|---|---|---|---|---|
| 4.5 | – | – | – | – | – | – | – | – | – |
| 4.5.1 | – | – | – | – | – | – | – | – | – |
| 4.5.2 | X | X | X | – | – | – | – | – | – |
| 4.6.11 | – | X | X | – | – | – | – | – | – |
| 4.6.2 | – | – | X | X | X | – | – | – | – |
| 4.72 | – | – | – | – | – | – | – | – | – |
| 4.7.1 | – | – | – | – | X | X | X | – | – |
| 4.7.2 | – | – | – | – | – | – | X | X | – |
| 4.8 | – | – | – | – | – | – | – | X | X |
Exchange 2013
| .NET | RTM- CU3 | CU4(SP1)- CU12 | CU13- CU14 | CU15 | CU16- CU18 | CU19- CU20 | CU21- CU22 | CU23 |
|---|---|---|---|---|---|---|---|---|
| 4.5 | X | X | X | – | – | – | – | – |
| 4.5.1 | – | X | X | X | – | – | – | – |
| 4.5.2 | – | X | X | X | – | – | – | – |
| 4.6.11 | – | – | X | X | – | – | – | – |
| 4.6.2 | – | – | – | X | X | X | – | – |
| 4.72 | – | – | – | – | – | – | – | – |
| 4.7.1 | – | – | – | – | – | X | X | – |
| 4.7.2 | – | – | – | – | – | – | X | X |
| 4.8 | – | – | – | – | – | – | – | X |
Notes
- When possible, bypass .NET Framework 4.6.1, as it not only requires updating the CU level before updating the .NET Framework, but also requires an additional hotfix: kb3146715 (ws2012r2), kb3146714 (ws2012) or kb3146716 (ws2008r2).
- .NET Framework 4.7 is not supported for any product level.
Usage
Suppose your organization loves procrastinating, and you are running Exchange 2013 CU6. Luckily, you run it on .NET Framework 4.5.1, which was already a supported configuration back in 2014 – yes, it’s been that long. Looking at the table, to get current with a minimal number of updates in mind, you can derive the following path:

The upgrade path to CU19 would therefore be:
- Upgrade to Exchange 2013 Cumulative Update 15
- Upgrade .NET Framework to 4.6.2
- Upgrade to Exchange 2013 Cumulative Update 19
- Upgrade .NET Framework to 4.7.1 (Optional)
Note that in addition to information being refreshed on Microsoft pages, the availability of older Cumulative Updates or .NET Framework updates might also change, so archive those files accordingly, if not for recovery of existing Exchange servers, then for this exact purpose.
Of course, you should stay as current as possible from a support and security perspective, making the above a non-issue. The reality is, some customers have reasons, legitimate or not, to be trailing with updates in their environment, and at some point may need guidance on how to proceed to get current. I hope this information helps in those situations.
Thoughts and feedback are welcome in the comments.
Update: On February 13th, Microsoft updated upgrade guidance on the Exchange Supportability Matrix page, stating:
“When upgrading Exchange from an unsupported CU to the current CU and no intermediate CUs are available, you should upgrade to the latest version of .NET that’s supported by Exchange first and then immediately upgrade to the current CU. This method doesn’t replace the need to keep your Exchange servers up to date and on the latest, supported CU. Microsoft makes no claim that an upgrade failure will not occur using this method, which may result in the need to contact Microsoft Support Services”.
This means you will be supported when upgrading along the revised upgrade path, but the risk remains. In the example above, when going from Exchange 2013 CU6 with .NET 4.5.1 to CU19, the support statement indicates you can upgrade to .NET Framework 4.7.1, when installing CU19. However, things might break, and you may need to contact support to get back into a supported, working situation. Therefore, I repeat my recommendation to download and archive CU and .NET Framework files, even if you are not planning to install them (yet).

 The Exchange Team
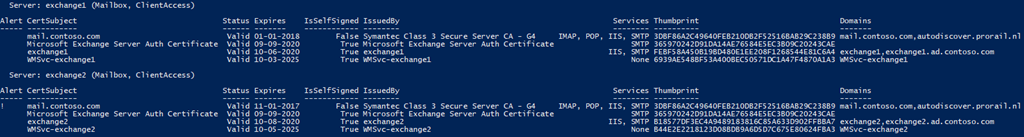
The Exchange Team  A quick tip on retrieving the expiration of certificates configured on your Exchange servers. While some certificate providers like
A quick tip on retrieving the expiration of certificates configured on your Exchange servers. While some certificate providers like