Last update: Version 3.17, September 8, 2023
Almost 3 years ago, I wrote an article on how to enhance the PowerShell Integrated Scripting Environment, or ISE. That seemed adequate for the Exchange admin back then, who would mostly connect PowerShell sessions to their on-premises environment, and occasionally a bit of Exchange Online.
Fast forward to 2015, most modern Exchange administrators not only require a connection – if any – to their Exchange on-premises environment, but likely to one or more of the Office 365 services as well, including Exchange On-Premises, Azure Active Directory, Exchange Online Protection, Microsoft Teams, Skype for Business Online, SharePoint Online, Azure Information Protection or Compliance Center.
All these services use a different PowerShell session, use a different endpoint FQDN, and in some cases require a locally installed PowerShell module. Likely common denominator is the credential used to access each of these services. So, tired of re-entering my credentials every time when switching from Exchange Online to Exchange Online Protection, I created a script with a set of functions to allow me connect to each individual Office 365 service or Exchange Online:
- Connect-AzureActiveDirectory: Connects to Azure Active Directory
- Connect-AIP: Connects to Azure Information Protection
- Connect-ExchangeOnline: Connects to Exchange Online
- Connect-SkypeOnline: Connects to Skype for Business Online
- Connect-EOP: Connects to Exchange Online Protection
- Connect-ComplianceCenter: Connects to Compliance Center
- Connect-SharePointOnline: Connects to SharePoint Online
- Connect-MSTeams: Connects to Microsoft Teams
- Get-Office365Credentials: Gets Office 365 credentials
- Connect-ExchangeOnPremises: Connects to Exchange On-Premises
- Get-OnPremisesCredentials: Gets On-Premises credentials
- Get-ExchangeOnPremisesFQDN: Gets FQDN for Exchange On-Premises
- Get-Office365Tenant: Gets Office 365 tenant name (SharePoint)
- Set-Office365Environment: Configures Uri’s and region to use
- Get-TenantID: Returns TenantID using previously used credentials
- Update-Office365Modules: Updates supported Office 365 modules
- Report-Office365Modules: Report on known vs online module versions
Note that functions and credentials used in the script are global, and in principle only need to be entered once per shell or ISE session. If you need different credentials, call Get-Office365Credentials again. User interaction is a very basic (Read-Host), but it does the job. The script will also detect if any PowerShell module supporting Multi-Factor Authentication is installed. If so, you will be prompted if for using MFA when authenticating to workloads such as Exchange Online, Azure Active Directory, Microsoft Teams, Skype for Business Online or SharePoint Online.
Requirements
During initialization, the script will detect the modules which are required for certain Office 365 services. When not installed, it will notify you, and provide a link where to obtain the PowerShell module. The related Connect function will not be made available. PowerShell is required to run this script, which is tested against version 5.1 (but should work with lower versions down to version 3).
Usage
The functions are contained in a script called Connect-Office365Services.ps1. You can call this script manually from your PowerShell session to make the functions available. However, more convenient may be to have them always available in every PowerShell or ISE session. To achieve this, you need to edit your $profile, which is a script which always starts when you start a PowerShell or ISE session. By default this file does not exist and you need to create it, including the path. Also note that the files for PowerShell and ISE are different, Microsoft.PowerShell_profile.ps1
and Microsoft.PowerShellISE_profile.ps1 respectively.
Now, of course you can copy and paste the functions from the script file to your own $profile. Better is to call the script from your $profile, as this allows you to overwrite the Connect-Office365Services.ps1 with updates. To achieve this, assume you copied the Connect-Office365Services.ps1 in the same location as your $profile, for example C:\Users\Michel\Documents\WindowsPowerShell. You can then make PowerShell and ISE call this script by adding the following line to the $profile scripts:
& “$PSScriptRoot\Connect-Office365Services.ps1”
Now when you start a PowerShell session, you might see the following:
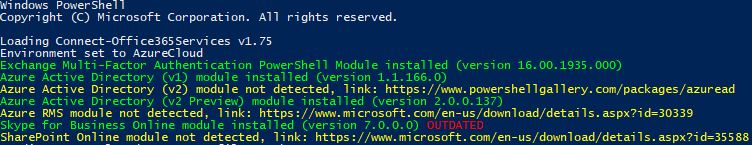
This shows the default environment is targeted (AzureCloud), the Exchange Modern Authentication PowerShell module as well as other modules mentioned in the example are installed. When online version checking is enabled (OnlineModuleVersionChecks variable), a check will be performed against the online repository, e.g. PSGallery, and outdated modules will be reported, like the Skype for Business Online module in the example. It’s also possible to automatically update modules setting the variable OnlineModuleAutoUpdate.
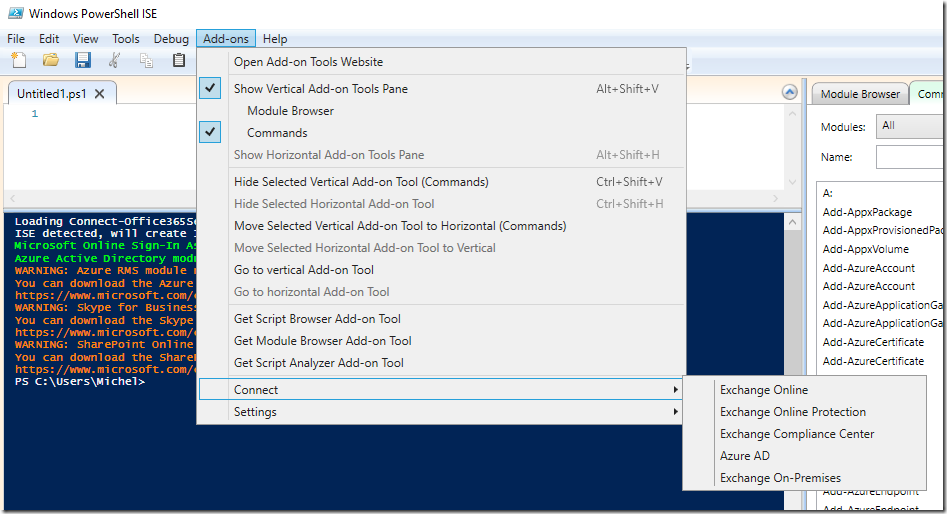
When you load the script from ISE, it will show something similar. However, it will also detect ISE and make connect functions available through the Add-On menu:
Notes
Customize this script to your liking. Note that for updating modules, you need to have administrator permissions on the local system.
Download
You can download the script from GitHub.
Revision History
Revision information is embedded in the source.
Feedback
Feedback is welcomed through the comments. If you got scripting suggestions, questions or want to report bugs, you can do this through GitHub or by using the contact form.


![iTunes-Podcast-logo[1]](https://eightwone.com/wp-content/uploads/2012/07/itunes-podcast-logo1-e1341277366970.png)


