Exchange on‑premises environments remain a critical part of many organizations’ messaging infrastructure. That also makes them frequent audit targets and attractive attack surfaces. Over time, configuration drift, mixed Exchange versions, and evolving security guidance make it increasingly difficult to keep the server compliant, especially in less strict managed environments.
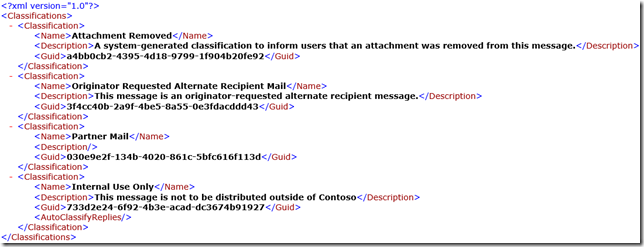
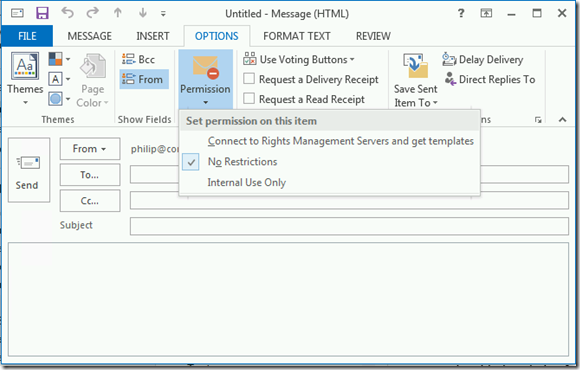
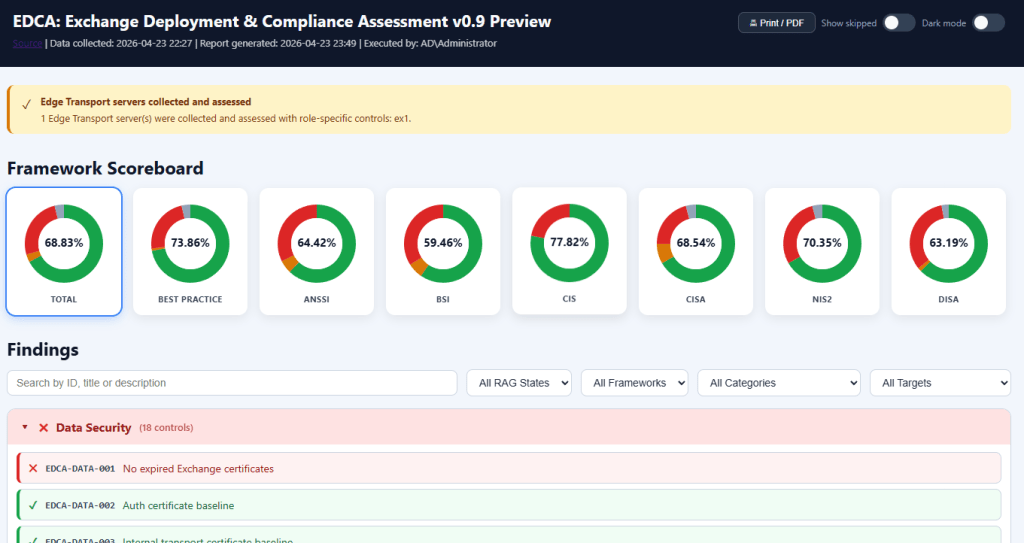
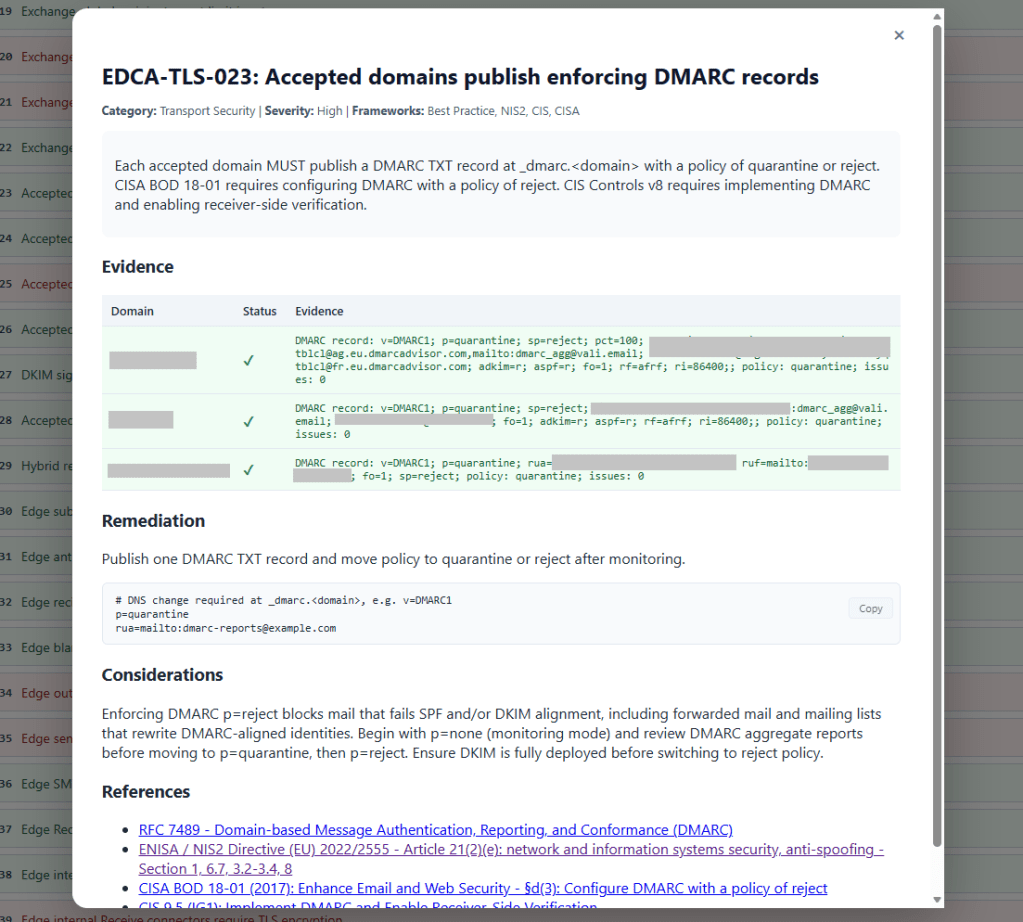
The Exchange Deployment & Compliance Assessment (EDCA) was created to answer that question with evidence. It’s a PowerShell-based assessment tool that collects information from Exchange servers and the Exchange organization. This information is then analyzed and evaluated against best practices and some well-known compliance control frameworks. The result is an (interactive) HTML report that can be used to check and monitor compliance, as well as to review remediation steps for each control. Edge Transport servers can also be added to the analysis; you only need to collect their data separately, as they are usually standalone servers. Their data file can then be added to the other data files to produce a single overview.
Key features
- Support for Exchange 2016, Exchange 2019, and Exchange Subscription Edition (SE)
- Evaluate Exchange Server on-premises with Mailbox Server and Edge Transport roles against 7 compliance frameworks, including common Best Practices.
- Produces an interactive HTML report with framework scoring, with options for filtering and searching.
- Reported controls provide context, impact, and remediation instructions.
- Option to generate a sample remediation script for failed controls (experimental).
EDCA is read‑only by design, not altering configuration items, changing system state, or automatically applying remediations. Even if controls can be automated (some cannot), the underlying process usually needs to follow a change process that also reviews the impact. The remediation steps or generated remediation script should be treated as a template with reviewable PowerShell sample code.
Usage
To run the EDCA tool, you need:
- The EDCA.ps1 main file.
- Config contains the controls information.
- Modules contains several scripts with helper functions.
Note: You can download the repository via the <> Code option by selecting Download ZIP.
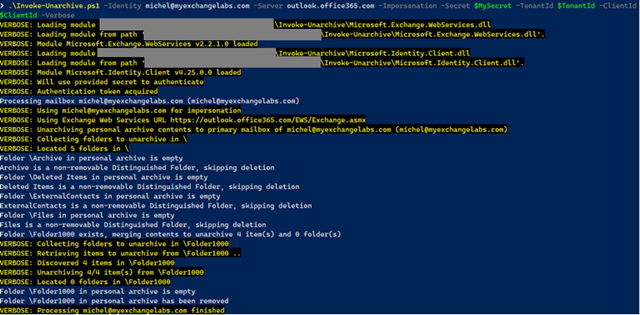
EDCA uses a collection, analysis, and reporting step. These steps are run when you do not specify any additional parameters when calling EDCA:
.\EDCA.ps1
When you run this on a server in an Exchange organization, provided you have sufficient permissions, it will discover all Exchange servers, collect information about Mailbox servers and the Exchange organization, and store this info in the Data subfolder. The generated Report will be stored in a subfolder named Output.
The other parameters of interest are:
- Local runs against the local Exchange server.
- Servers run against specified Exchange servers.
- Throttlelimit will limit the number of Exchange servers being interrogated in parallel.
- Report produces a Report using data collected or, when Collect is not specified, using info from the Data subfolder.
- Framework to limit the Frameworks being used to report on.
- RemediationScript to generate a template to remediate failed controls.
Frameworks
| Framework | Official Reference(s) | Official URL |
|---|---|---|
| Best Practice | Common best practices for Exchange Server deployments, including CSS Exchange | – |
| ANSSI 🇫🇷 | Mise en œuvre sécurisée d’un serveur Windows Recommandations de sécurité relatives à TLS Sécuriser la journalisation dans un environnement Microsoft AD Transition post-quantique de TLS 1.3 | messervices.cyber.gouv.fr |
| BSI 🇩🇪 | IT-Grundschutz-Kompendium Edition 2023 Modules: SYS.1.1 · SYS.1.2.3 · APP.2.2 · APP.5.2 | bsi.bund.de |
| CIS 🇺🇸 | CIS Microsoft Exchange Server 2019 Benchmark CIS Microsoft Windows Server 2019/2022 Benchmark CIS Controls v8 | cisecurity.org |
| CISA 🇺🇸 | Microsoft Exchange Server Security Best Practices Guide Advisory AA21-062A: Mitigate Exchange Server Vulnerabilities Binding Operational Directive 18-01 Known Exploited Vulnerabilities Catalog | cisa.gov |
| DISA 🇺🇸 | Microsoft Exchange 2019 Mailbox Server STIG Microsoft Exchange 2016 Mailbox Server STIG | public.cyber.mil/stigs |
| NIS2 🇪🇺🇳🇱 | NIS2 Directive (EU) 2022/2555 NCSC-NL TLS Guidelines 2025-05 | eur-lex.europa.eu ncsc.nl |
Feedback
EDCA is currently released as a preview. I strongly recommend using it in test or lab environments first, especially while controls, scoring, and reporting continue to tweaked and evolve. Feedback is very welcome. If you encounter issues, have suggestions, or want to propose additional controls or improvements, please use GitHub.
Downloading
The project is open source and available on GitHub at https://github.com/michelderooij/EDCA.
Questions?
The README.MD contains some more details on permission requirements, connectivity requirements, usage examples, and the latest updates.