Yesterday, an article was published on ZDNet, where the author claims “Russian Cyberspies” are exploiting a backdoor in Exchange. The article is based on a report of Slovakian-based ESET Research, which is no stranger on the anti-virus/malware market. The report, titled “Turla LightNeuron, One email away from remote code execution”, claims the group – Turla – leverages LightNeuron to exploit Exchange Server for malicious usage, using instructions hidden in image attachments delivered through e-mail to control the backdoor. The news was quickly picked up by other media, and it didn’t take long for customers to start asking questions on the topic. Time for some fact checking.
Yesterday, an article was published on ZDNet, where the author claims “Russian Cyberspies” are exploiting a backdoor in Exchange. The article is based on a report of Slovakian-based ESET Research, which is no stranger on the anti-virus/malware market. The report, titled “Turla LightNeuron, One email away from remote code execution”, claims the group – Turla – leverages LightNeuron to exploit Exchange Server for malicious usage, using instructions hidden in image attachments delivered through e-mail to control the backdoor. The news was quickly picked up by other media, and it didn’t take long for customers to start asking questions on the topic. Time for some fact checking.
Exchange Backdoor
The article claims the group using ‘one of the most complex backdoors’ ever spotted on an email server. While complexity is relative, it could very well be that this backdoor was indeed discovered on some improperly managed Exchange Servers in the wild.
However, the exploit leverages an installed malicious MTA (Message Transfer Agent, or Transport Agents in Exchange). An MTA is software handling incoming and outgoing e-mail messages using the Simple Mail Transfer Protocol (SMTP). A lot of legitimate 3rd party MTAs exist for Exchange Server, for example to add disclaimers to messages or for message hygiene purposes.
This LightNeuron is the actual backdoor, so there is no backdoor in Exchange. A totally different conclusion than one could read from the article’s title, and a totally different attack vector:
- How did this Transport Agent get installed on Exchange server in the first place?
- How was it possible to store the DLLs required by the Transport Agents, and which are likely to get caught by AV products, on Exchange Server?
- How was it possible to perform these tasks using administrative access, which is required to install such components in the first place?
The ESET report mentions this requirement; the ZDNET article and all other media simply omit this. Note that developing your own Transport Agent isn’t rocket science; Microsoft provides instructions on how to write your own custom Transport Agent for Exchange Server on-premises.
Hidden Instructions
Sending instructions hidden in images isn’t new. Steganography became famous to public in the last decade, where Osama Bin Laden was claimed to be embedding instructions for his followers in images posted on the internet. Little messages can also easily be embedded in the structure of an image file format, with places to store custom data or instructions.
Remote Control
As the installed malicious MTA runs under administrative permissions, it is no surprise that whoever (remotely) controls the MTA, in principle controls the Exchange Server as it runs in the context of the Exchange Trusted Subsystem.
Remote Controlled malicious code is not new; it is what drives zombie computers, and it is what made some prank tools popular in the mid-90’s, when you could prank your coworkers by opening their CD trays (anyone remember those?).
Impact
ESET claims that Turla has been leveraging LightNeuron for nearly 5 years, “which shows the tool’s advanced capabilities, being able to avoid detection for so many years”. In my opinion, this shows how many organizations have more bigger issues, such as an improperly managed mail environment.
SendMail
The report also mentions LightNeuron being ported to *NIX as well, e.g. SendMail. This shows perfectly that any communications system, when compromised, can be used for man-in-the-middle attacks. However, mentioning leaks in SendMail might not drive traffic as much as mentioning ‘Backdoor in Exchange’ for media, which is a driver when you depend on advertisements.
Detection
The article claims the hidden messages make LightNeuron hard to detect. Of course, this depends. The backdoor requires installation and presence of two malicious DLL files. Any respectable AV product should catch those. Windows Server 2016+ comes with Windows Defender, which according to its encyclopaedia should be able to detect Turla variants.
Removal
Finally, the article claims that, “removing this backdoor is quite problematic”. This is utter nonsense, as any weathered Exchange administrator should be able to install or uninstall Transport Agents as part of their skill set.
Conclusion
In summary and concluding:
- This is not a backdoor in Exchange Server.
- The backdoor is a malicious Transport Agent which needs to be installed on the Exchange Server
- Installing this backdoor requires administrative permissions.
- Well-managed Exchange environments should be OK.
- Removal is simple, and a task any Exchange admin should be able to perform.
- Windows Defender detects Turla variants.
And last but not least:
- Media should do proper fact-checking as opposed to blindly copying articles.
- Media should use titles which reflect the contents, and refrain from click-bait titles.
- ESET is a vendor selling e-mail hygiene and security-related products, which always is a potential red flag when these kinds of reports are published.

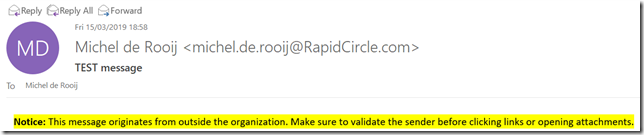
 A little notice on a potential helpful feature which was introduced to Outlook at some point, but I wasn’t aware of before (or it’s just new). At least the option is available in Outlook v1905 build 11629.20008 C2R; it might also be available in standalone.
A little notice on a potential helpful feature which was introduced to Outlook at some point, but I wasn’t aware of before (or it’s just new). At least the option is available in Outlook v1905 build 11629.20008 C2R; it might also be available in standalone.

 Updated April 12th: Notice on KB4487563
Updated April 12th: Notice on KB4487563